With an IIoT network that covers the entire enterprise and has dozens of machines connected to a centralized system, you can see why it’s so tempting for cybercriminals to attempt access on your network. On the other hand, it also shows where your weaknesses are and what you can do to protect it.
During recent years, healthcare, financial service, and retail industries were more “interesting” to cyber attackers than the manufacturing industry. As business disruption and intellectual property theft emerge, more and more manufacturers are becoming victims of cybercrime.
What is Behind the Attacks?
The 2018 Verizon Data Breach Investigations Report shows us that state-sponsored attackers caused more than half of the data breaches in manufacturing, and leading motive was cyberespionage. Due to the fast convergence of OT and IT networks in these manufacturing companies, they exhibit a higher rate of cyberattack activity.
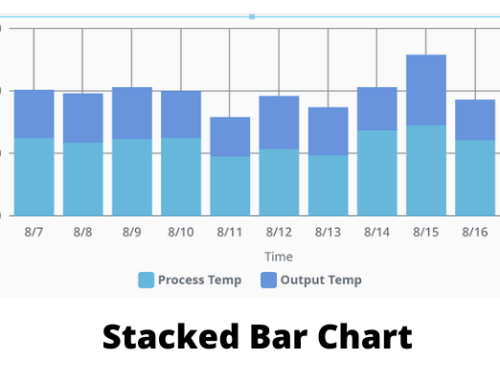
The massive loads of data were collected from January to June 2018, from millions of workloads and devices from the data center, customer cloud, and enterprise environments. They show three findings that are of most interest to cyber attackers. They are the way data is stolen from manufacturing networks, the volume of internal movement between systems, and the frequency of external remote access.
Data Exfiltration
With multiple sensors that aggregate data at the IIoT network’s gateway and send it to a cloud database, an IIoT network architecture doesn’t typically indicate a cyber attack. This data exfiltration behavior is sometimes related to other threat behaviors that can point to an assault in progress. Organizations must ensure that systems are sending data to the approved and intended external systems instead to the attackers who want to steal critical assets.
Internal Movement between Systems
There are many gateways (connected to each other for a better peer-to-peer communication) in a manufacturing network that communicate with smart machines and devices. To map out a manufacturing network and find critical assets to steal, cyber attackers use the same self-discovery used by those peer-to-peer devices. Cyber attackers can thus move laterally across the entire system until they find a way to complete their mission. That type of cyber attacker behavior is known as internal reconnaissance and lateral movement. If a higher-than-normal rate of lateral movement or malicious internal reconnaissance behavior is detected, it’s an indicator of possible attacks on the network.
External Remote Access
When an internal host device connects to an external server, it is known as external remote access. One of the most common command-and-control behaviors in manufacturing is the use of external access tools. This process is also a gateway for attackers to infiltrate a network by hijacking an external remote access connection.
What Can You Do About It?
Manufacturers used to rely on exclusive and customized protocols that made it harder for attackers to mount an attack. However, after the conversion from proprietary to standard protocols, it has made it easier for them to steal, spread, and spy. Today’s factories have Internet-enabled production lines that support remote management and data telemetry. It connects their IIoT machines to networks that rely on communication with enterprise applications and computing devices.
Systems critical for supply-chain processes and thin production lines need to have the best security access controls that can isolate a manufacturing system (however, most manufacturers don’t invest in them for economic reasons.) Real-time monitoring and network visibility are vital for identifying the earliest signs of cyber attacks in any infrastructure of this kind. Also, security analysis should be performed frequently.
Cybersecurity is today’s number one problem for organizations that rely on IoT. To enhance existing cybersecurity teams, we need to use artificial intelligence solutions to detect and respond to cyber threats faster and help stay ahead of cybercriminals.